Today, you need to have complete control over potential network problems, especially when it comes to security . Also, have a global overview of them: the causes, the impacts on daily tasks and the solutions that could be applied. The times are running, forcing connectivity to be reliable and provide protection against multiple threats . To the latter we must add the fact that work from home is booming, and all those who practice telework must be protected.
Network security and its management are evolving favorably thanks to tools that make everything much easier and more practical. Gone are the days when multiple solutions, very expensive and difficult to use, did not give the desired answer. Cyber attacks are giving less and less truce and the networks have to have a real protective shield.

Zeek is presented as a tool to support the management of response to security incidents . It works by supplementing signature-based tools to find and track complex network events. It is characterized by providing fast responses, in addition to using multiple flows and protocols. It not only helps identify security events, but also aims to facilitate troubleshooting.

Detailed monitoring of networks using logs
A log file is of great help when analyzing network problems of all kinds, including those events that compromise its security integrity. Zeek takes very good advantage of this, offering a file that summarizes a good part of the logs it can generate, based on various protocols. Some of the protocols that we can cite are:
- DHCP
- DNS
- FTP
- HTTP
- SNMP
- SMTP
- SSL and many more
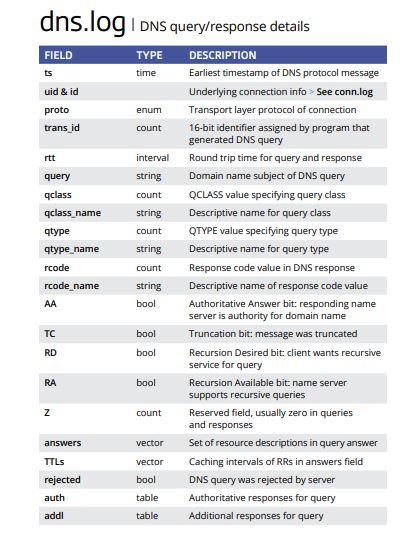
Above we see a screenshot of all the fields contained in the log of DNS connections. It is possible to see that each field details the type of data that can be viewed and a brief informative description. Let’s cite a few fields as examples:
- trans_id: a unique number generated to identify the generated log.
- rcode: value of the DNS response code.
- rejected: this is a boolean value field (true or false) that tells us if the DNS connection request was rejected or not.
One aspect that is generally commented on with regard to logs is that they are extensive and complicated to understand. Through this support material , you will be able to better understand the content of the logs and achieve control of security events.
Monitoring scripts
Another facility that we can highlight from Zeek is that it is possible to have some pre-configured and ready-to-use scripts. They are used to execute own network monitoring activities, which are used frequently, so you will save time.
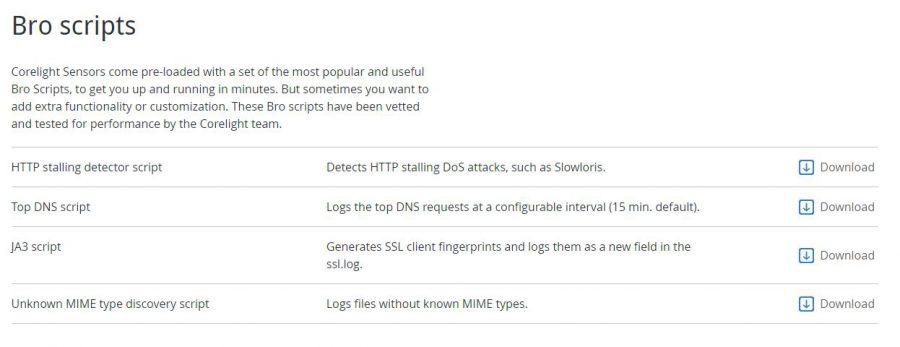
One of the scripts that we can highlight is the one that corresponds to the HTTP Stalling Detector . This is used to detect HTTP Stalling type DDoS attacks, to get an idea, this type of DDoS takes advantage of one of the most relevant errors of a web server.
It consists of not being able to determine if a remote client is connected to the server through a slow connection link. Or, if the same client is sending data without any control at very slow speed. Consequently, the web server cannot generate a timeout to cancel that connection after a certain time, or simply terminate it. If a web server has limited capacity, it can be easily affected by these types of attacks.
If you want to take advantage of this or other scripts, you must enter the official portal of the Corelight company, which supports Zeek, to access them through its official Github repository. Other resources are also available on the same site to help you get started using the tool.
Curiosity about Zeek
When you hear or say the word “Bro,” what makes you think? Does the word “Bromance” or “Bro Culture” ring a bell? As we have discussed, the Zeek program was previously called Bro . However, the meaning of the word “Bro” in popular jargon applies to contexts that have little or nothing to do with the focus of this computer security solution. This is so to the point that the company that develops this solution has run into risks that potential or current customers may have misconceptions regarding the original purpose in which said solution had remained.
Consequently, by a decision made by the leadership team, it was decided that the name change. Zeek, in fact, is a name that already existed in the minds of the first group of people who had started working on the project. So they have not taken too long to find a substitute name.
How to download Zeek
Access this link to get all the downloads you need. You will have the source code of the current stable version, as well as the previous version that will have support until October of this year. In short, you will obtain the necessary documentation to have the necessary support, as well as an active community that contributes frequently so that Zeek continues to improve.
If you are not sure whether or not to opt for this tool, they have an online application that allows you to test some basic functionalities in real time. By entering this link, you will not need an account to test. You will have a brief explanation of each unit and a space to test the commands and codes.