On more than one occasion you have surely found yourself in the position of downloading an installation profile. Unfortunately this is a part of the system that can become unknown, being a real risk for security. To prevent you from installing something that is unknown to you, we will tell you everything you need to know about the configuration profiles in this article.
What are configuration profiles
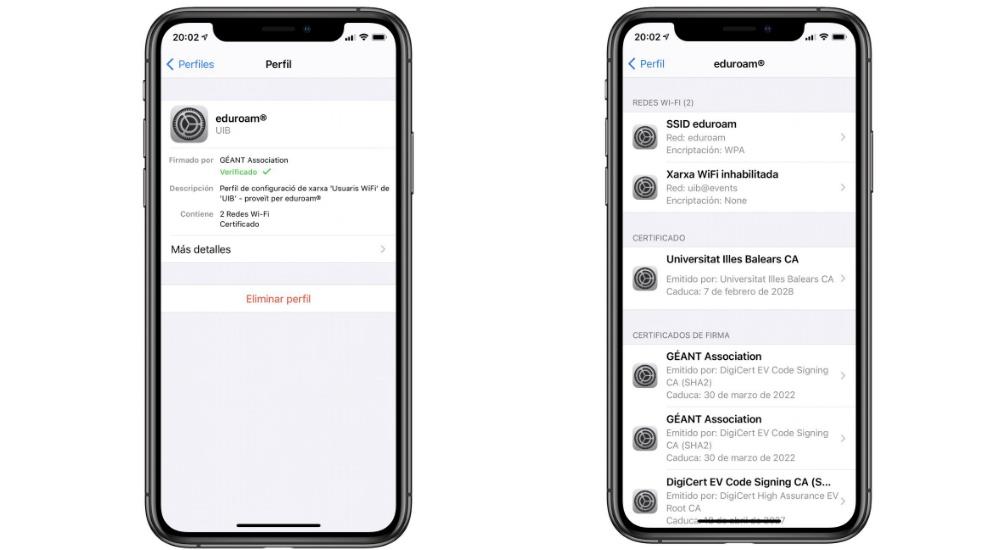
Configuration profiles are a tool that gives system administrators the necessary tools to configure other devices in a unified way. The possibilities they offer are many, from making changes to the basic configuration to enabling data plans or applications that can only be on a specific device. All of this is developed from the utility program that can be found in Windows or macOS. Once done, you can choose to upload it to be verified by Apple itself and to be trusted. This is something basic that guarantees your safety, something that we will discuss below.

Installing the profiles
Before installing a profile, you must have it downloaded on your devices. The download is quite simple since you simply have to follow a specific link that the developer sends you or receive a simple SMS. Once it is downloaded, you must bear in mind that you can only have a single profile in the queue and that it has a durability of 8 minutes. Once you have taken this into account, to install a profile you simply have to follow the following steps:
- Go to the ‘Settings’ app.
- At the top you will see the word ‘Downloaded profile’ on which you must click.
- After consulting all the information in the certificate, you can install it and restart the device.

The function they have in the day to day
If you have ever tried a beta of iOS or iPadOS, surely you have seen the need to install one of these profiles. This is undoubtedly the most common use for the vast majority of users. With these profiles of Apple itself, it is possible to have the appropriate internal configuration so that it can connect to the company’s servers and download the specific beta file. But beyond the software betas, it is also used for many other uses.
Among these uses, the business and educational field stands out above all. A company or university usually has a WiFi network that is common to everyone and that requires a certain connection to a specific server to verify the credentials. This process that can be very tedious to do by hand, when editing the network options it can be done automatically with the configuration profiles. When installed, all the devices from the same institution will have a similar configuration, saving many headaches. Within a company, for example, they can be applied to the following tasks:
- Define passwords.
- Create trusted certificates and credentials.
- Add internal calendars.
- Create trusted web shortcuts.
- Manage credentials for the SCEP protocol.
- Restrictions on purchases, create backup copies, do not allow screenshots …
Risks of installing them
As we have commented previously, the purpose of the configuration profiles is to modify the settings of a device. A priori it has important utilities as we have seen but it can also be a gateway for hackers. With a simple profile you can get access to the guts of the device and do whatever you want with it without you even noticing. That is why the use of these profiles has to be very controlled and not install any type of profile that comes your way.

Ensuring security on the iPhone or iPad is basically achieved by not trusting everything that is online. Through different websites or possibly emails you will receive different profiles that promise to do something that is impossible, such as having free applications or customizing all the aesthetics of the device. With this premise it is possible that they end up taking over your device. That is why the phrase ‘here the best antivirus is yourself’ applies here. You should always assess whether it is necessary to have the profile installed. And if it is, always check that the signer is trusted. Apple always adds a small ‘tick’ in those profiles that have been approved by the brand’s team. These in principle are the only ones that you should have installed.
It is for all this that entering the device with these profiles is somewhat dangerous. In general, it is better not even to get close to it, I do not know that you know perfectly what you are doing.